Issues around cyber security are nothing new for companies in the digital age but considering the recent headlines around the Cambridge Analytica scandal and the Equifax Credit Reporting hack, a new emphasis on how we in commercial real estate think about data protection might be warranted. Data breaches commonly involve the taking of consumer data, trade secrets, and other financial information. The damage to a company’s reputation and potential legal liability (class action lawsuits are a common remedy to harmed consumers) are already significant but the potential for physical damage inside a property is unique to the built environment. The assessment of physical security risks in a property is commonly talked about with regard to protecting tenants. Controlling building access, providing security and monitoring parking garages are all key parts of property management but what about protecting tenants from cyber-attacks and other digital threats?
Various types of property management software are becoming more integrated with cloud technology and other types connected platforms and many building owners might not be aware of the vulnerabilities created as a result of implementing new technologies.
In a property, the interconnectedness of connected devices, HVAC systems and other industrial control systems, and open Wi-Fi networks increase data vulnerability and potential likelihood of attack. Intelligent buildings tend to be interlinked with tenant systems, creating exposures to tenants whereby their systems and data can be accessed through the CRE owners’ IT systems. [1] This interconnectedness isn’t always fully appreciated by the owner, property manager and tenant and potential legal liability can often be unknowingly shared among those groups.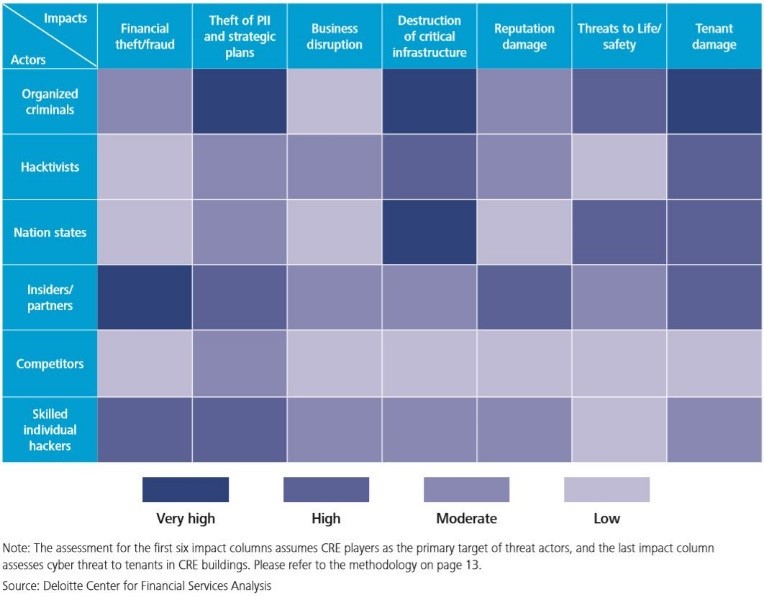
The Target Corporation’s data breach in November 2013, happened because the hackers were able to find a route through the company’s HVAC contractor’s systems to steal payment card records and other personal information of nearly 110 million customers. Along with reputation damage, the company reported a gross financial loss of $252 million by the end of 4Q14. The incident highlights that the IT systems of CRE owners can act as an entry point for hackers to access tenant data, and that they are becoming an increasingly integral part of a tenant’s supply chain. [1]
Unlike like other victims of a cyber-attack, the nature of physical real estate dictates that victims could be physically harmed. An HVAC hack in a data center could change the temperature enough to destroy critical servers, a retail center could have its security systems taken down long enough to facilitate a robbery or imagine the confusion and destruction if fire sprinklers went off on a trading floor in Manhattan. These scenarios are particularly dramatic but consider that other attacks have similar impact but can go undetected. Many companies have been hacked and don’t currently know it. In late September 2014, a large US real estate investment trust (REIT) discovered that its systems containing personal information and key company information had been compromised by a cyber intrusion, but the actual data breach happened months earlier.2 The company recorded a $2.8 million cyber intrusion expense, including investigative fees and identity protection services but the company has yet to fully understand the motive for the attack, the exact data that was compromised, and the full amount of damage. [2]

The chart below shows the potential types of bad actors versus the damage they’re most likely to cause. Beginning to understand what types of information these individuals could be after is the first step in constructing a methodology to prevent these events from succeeding. Being able to monitor, detect and understand the nature of the compromise of the intrusions is critical to being able to recover.
Unfortunately, far too few in the commercial real estate industry have developed a sophisticated methodology for countering threats to in their properties and the response required to remedy the potential damage caused by a cyber-attack. As adoption of new digital tools evolves and the headlines continue to report new hacks, executives in real estate will eventually be forced to adopt their own governing rules and policies to ensure their properties and tenants are protected.
How do you view cyber security with your buildings? What threats to your area of commercial real estate do you see that aren’t adequately addressed?
Source:
- Sheth, S. (n.d.). Deloitte Center for Financial Services (2015 ed.). Deloitte Services India Pvt. Retrieved March 1, 2018, from https://www2.deloitte.com/content/dam/Deloitte/nl/Documents/real-estate/deloitte-nl-real-estate-evolving-cyber-risk-re-predictions.pdf.
- Gardner, R. and Brown, M. (2015). Managing real estate cybersecurity. [online] Ey.com. Available at: http://www.ey.com/Publication/vwLUAssets/ey-managing-real-estate-cybersecurity/$FILE/ey-managing-real-estate-cybersecurity.pdf [Accessed 3 Apr. 2018].

